Regex to match executing a stored procedure within a stored procedure
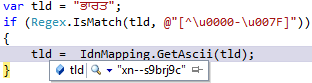
Unless you’re working with a custom string format, which requires you writing a regular expression, I suppose (suggest?) you’ll look it up online, right? If you need a Regex to match an IP, MAC or an E-mail, would you spend time writing it? Chances are that you might leave room for false positives and/or false negatives, unless you really test it. That’s why it’s common to look it up online. I needed to take a list of proc names and parse thousands of create procedure scripts, looking up if anything from the input list was used (executed) from those procs. A procedure executing another procedure. ...